Documentation Index
Fetch the complete documentation index at: https://docs.dynamic.xyz/docs/llms.txt
Use this file to discover all available pages before exploring further.
Setting up Webhooks
Events
Identify what events you would like to monitor here.
Enable
Register your endpoint with Dynamic using the Webhooks Developer Dashboard or the API.
Signature validation
Dynamic follows general best practice when it comes to signature validation. As such, each payload includes ax-dynamic-signature-256 header which has a hash signature value, generated from your secret token.
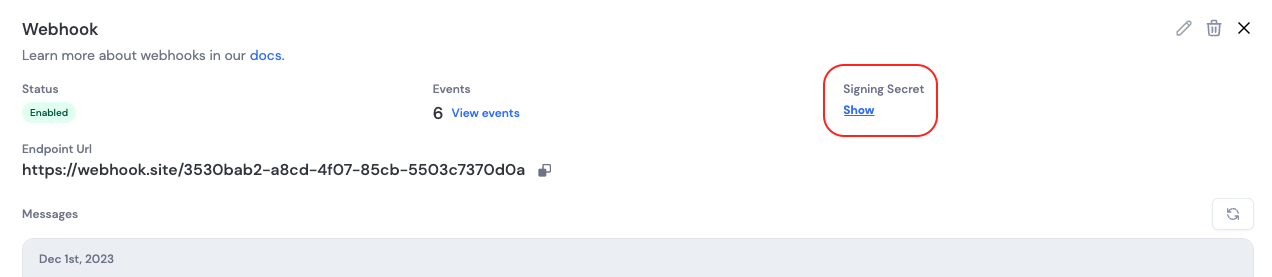
Each webhook has a unique secret token that is used to generate the message signature from the event object. This secret can be found on the webhook detail page in the Developer Dashboard.
x-dynamic-signature-256 header to an HMAC-SHA256 of the raw request body using your webhook secret. Use a constant-time comparison to avoid timing attacks.
The structure of the payload object must match exactly how the message was sent; otherwise signature verification will fail.
x-dynamic-signature-256 header, and the parsed JSON body to verifySignature. Only process the event if it returns true. For other languages, the same approach applies (HMAC-SHA256, constant-time compare); see GitHub’s webhook validation guide for a similar format.
Next Steps
- Learn about Event Delivery & Best Practices for production implementation
- Review the Event Types to understand what events you can monitor